How to Build an Audit-Ready Cloud Environment
For any organization to have an audit-ready cloud environment, a baseline which contributes to any compliance program such as SOC2, FedRAMP, and HiTrust, it is essential to follow best practices for a well-architected environment and security when building the cloud environment.
The security best practices include:
● Confidentiality: Allow access to resources and applications only to those who meet the appropriate security criteria. Granular access to IAM user and roles should be the most highly guarded, for example, through the use of AWS Systems Manager Parameter Store and Secrets Manager.
● Integrity: Integrity is the assurance that the information being accessed has not been altered and truly represents what is intended. Information can lose its integrity through malicious intent, such as unauthorized changes or intentional misrepresentation. Integrity can also be lost unintentionally, such as when a computer power surge corrupts a file, or someone authorized to make a change accidentally deletes a file or enters incorrect information. Regardless of the cause, changes and status needs to be tracked, and a record log used to itemize events. AWS Cloudtrail is a good way to accommodate this.
● Availability: Infrastructure should be available 24/7 with Multi-Availability Zone (AZ) deployments and a well-structured disaster recovery design, including database load balancing using Amazon RDS, and high-availability storage options through Amazon S3, etc.
● Controllability: Regulations like GDPR require that companies encrypt both data in transit and data at rest. Ibexlabs’ solutions are designed with encryption for both.
● Visibility: Application and data should feature Well-Defined Tags that help you identify resource characteristics and their purpose. This can be achieved with the help of AWS Config which provides a greater degree of visibility. The information is stored centrally with high security using IAM and encryption.
● Agility: The entire architecture should be built with Infrastructure as Code (IAC) following security best practices with multiple reviews and tests. When updating the architecture, AWS security guidelines should be prioritized.
● Automation: Fully automated CI/CD pipelines can deploy the application with pull requests created by developers in different environments with the use of Jenkins.
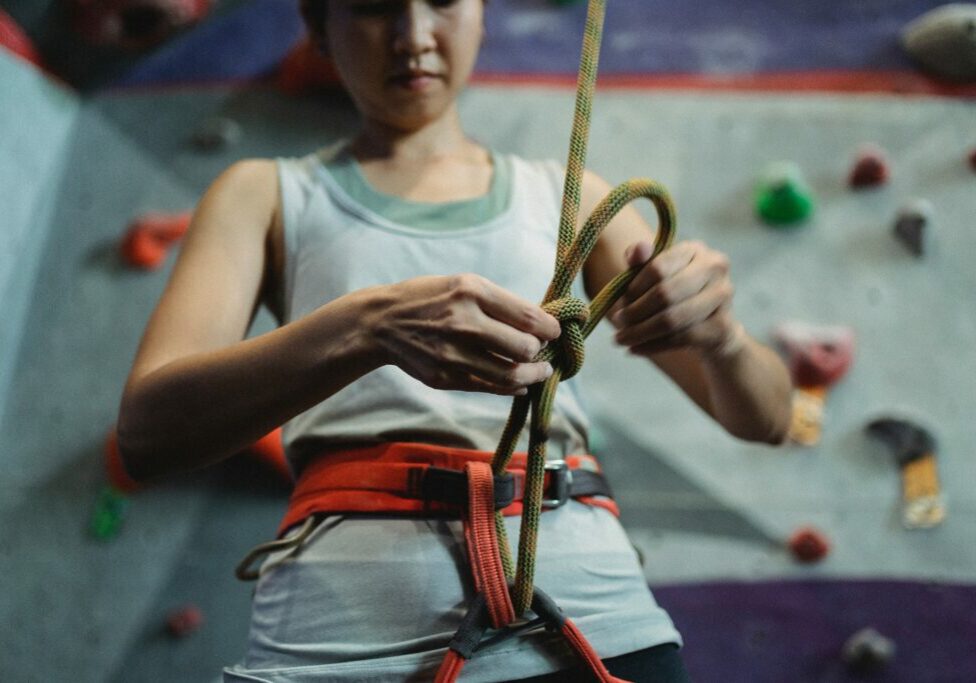
● Backups: Another essential tool for information security is a comprehensive backup plan for the entire company. Not only the data on the corporate servers, but individual computers used throughout the organization as well should have a proper backup.
● Virtual Private Networks: A virtual private network extends a private network across a public network. The server hosting the VPN should be secure: it should only be accessible from a specific IP range and have encryption at rest and encryption in transit (HTTPS) with SSL.
● Firewalls: A firewall should be configured at every part of the Network, Compute, and Application levels with strict rules. AWS WAF solution firewall protection can be added to the application endpoint for regional and global resources where the application is served. This will protect your web applications or APIs against common web exploits that may affect availability, compromise security, or consume excessive resources.
● Network Access Control Lists (ACL) should be utilized as an additional layer of security for your VPC that acts as a firewall for controlling traffic in and out of all subnets where the system resides. DDoS attacks can be mitigated at the subnet level by blocking any set of IP addresses at any time by creating rules.
● Intrusion Detection with AWS Guard Duty allows for alert findings to be sent to different channels of communication including Slack.
● Safeguarding Personally Identifiable Information (PII): AWS Macie uses machine learning and pattern matching to discover and protect sensitive AWS data, and PII. It provides several means of alerts for application-level threats and includes support for third-party solutions.
Assess your Audit Readiness with AWS Audit ManagerOften, organizations struggle to build well-architected environments that meet auditory compliance. They can work for months scanning the environment to find the system elements that are not compliant with the required standards. With the lack of cloud expertise and knowledge this task becomes even more challenging as the environment scales. This can be solved by using AWS Audit Manager.

AWS Audit Manager makes the audit process easy by letting you create audit assessments from the prebuilt assessment templates that contain industry-standard compliances. It automates the evidence collection which greatly reduces the time spent on manual intervention. The audit capability scales along with the growing business. The prebuilt frameworks help move evidence from cloud services into auditor-friendly reports by mapping your AWS resources to the selected industry requirements or regulations. It collects and organizes relevant evidence from the AWS accounts and resources, such as resource configuration snapshots, user activity, and compliance check results.Audit Manager continuously collects data from the AWS services used and generates reports with evidence necessary to demonstrate compliance with control requirements.AWS Audit Manager also ensures the integrity of these reports and evidence by securely storing and validating evidence in its own managed storage repository with specific user-level permissions.As demonstrated above, audit preparation is detailed and complex. Ibexlabs has deep experience with AWS cloud protocols and audits. Contact us to know how we can help you prepare for industry aligned inspections, and remain vigilant against the innumerable cyber and related security threats.